- Home >
- Services >
- Access to Knowledge >
- Trend Monitor >
- Type of Threat or Opportunity >
- Trend snippet: This threat landscape paper provides valuable insights into emerging trends in terms of cybersecurity threats, threat actors’ activities as well as vulnerabilities and cybersecurity incidents.
Trends in Security Information
The HSD Trendmonitor is designed to provide access to relevant content on various subjects in the safety and security domain, to identify relevant developments and to connect knowledge and organisations. The safety and security domain encompasses a vast number of subjects. Four relevant taxonomies (type of threat or opportunity, victim, source of threat and domain of application) have been constructed in order to visualize all of these subjects. The taxonomies and related category descriptions have been carefully composed according to other taxonomies, European and international standards and our own expertise.
In order to identify safety and security related trends, relevant reports and HSD news articles are continuously scanned, analysed and classified by hand according to the four taxonomies. This results in a wide array of observations, which we call ‘Trend Snippets’. Multiple Trend Snippets combined can provide insights into safety and security trends. The size of the circles shows the relative weight of the topic, the filters can be used to further select the most relevant content for you. If you have an addition, question or remark, drop us a line at info@securitydelta.nl.
visible on larger screens only
Please expand your browser window.
Or enjoy this interactive application on your desktop or laptop.
This threat landscape paper provides valuable insights into emerging trends in terms of cybersecurity threats, threat actors’ activities as well as vulnerabilities and cybersecurity incidents.
The ENISA Threat Landscape (ETL) report, now in its eleventh edition, plays a crucial role in understanding the current state of cybersecurity mainly within the European Union (EU). It provides valuable insights into emerging trends in terms of cybersecurity threats, threat actors’ activities as well as vulnerabilities and cybersecurity incidents. Accordingly, the ETL aims at informing decisions, priorities and recommendations in the field of cybersecurity. It identifies the top threats and their particularities, threat actors’ motivations and attack techniques, as well as provides a deep-dive insight on particular sectors along with a relevant impact analysis. The work has been supported by ENISA’s ad hoc Working Group on Cybersecurity Threat Landscapes (CTL).
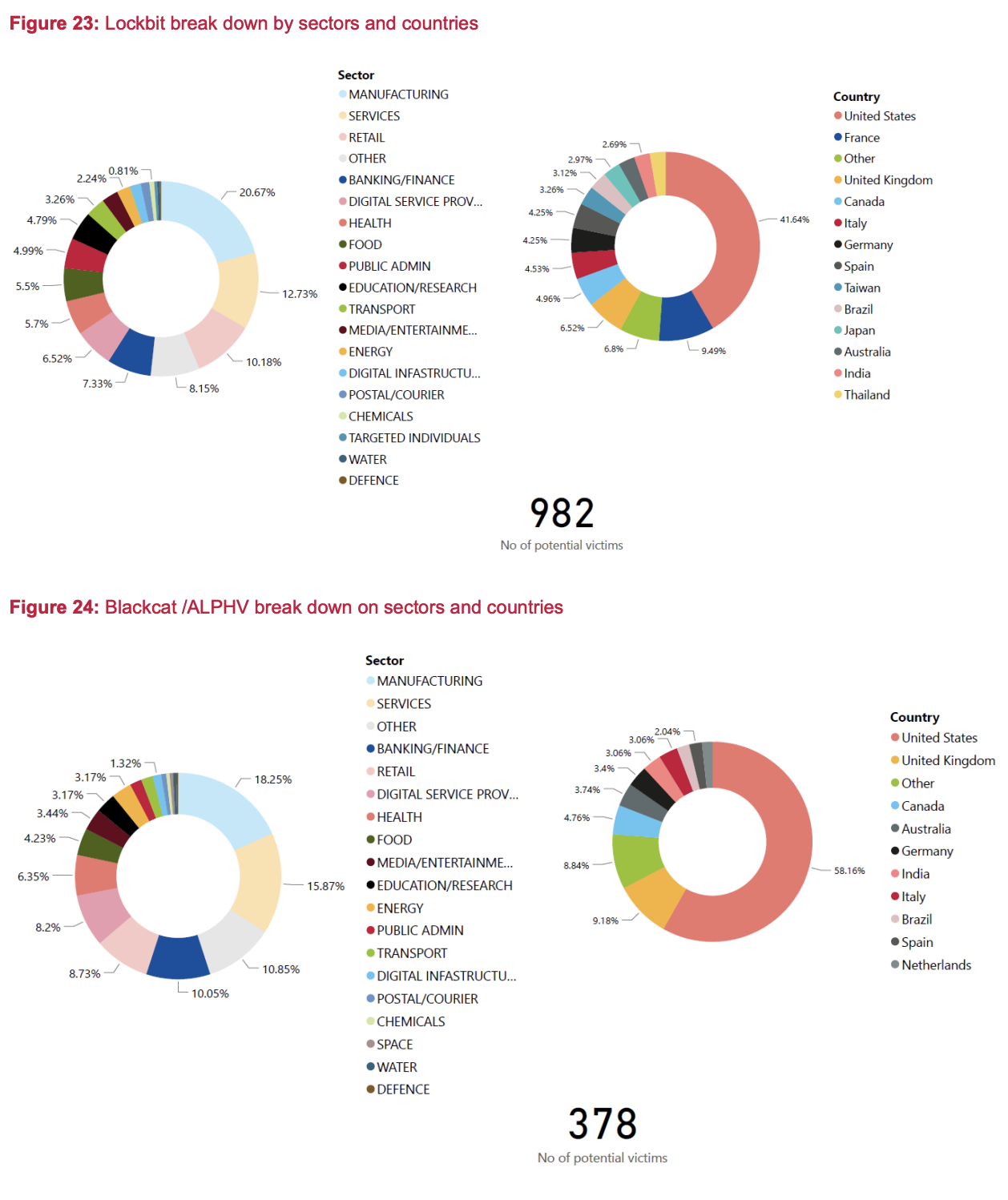
In the latter part of 2022 and the first half of 2023, the cybersecurity landscape witnessed a significant increase in both the variety and quantity of cyberattacks and their consequences. The ongoing war of aggression against Ukraine continued to influence the landscape. Hacktivism has expanded with the emergence of new groups, while ransomware incidents surged in the first half of 2023 and showed no signs of slowing down. The prime threats identified and analysed include:
• Ransomware • Malware • Social engineering • Threats against data • Threats against availability: Denial of Service • Threat against availability: Internet threats • Information manipulation and interference • Supply chain attacks
For each of the identified threats, we determine impact, motivation, attack techniques, tactics and procedures to map relevant trends and propose targeted mitigation measures. During the reporting period, key findings include:
• DDoS and ransomware rank the highest among the prime threats, with social engineering, data related threats, information manipulation, supply chain, and malware following.
• A noticeable rise was observed in threat actors professionalizing their as-a-Service programs, employing novel tactics and alternative methods to infiltrate environments, pressure victims, and extort them, advancing their illicit enterprises.
• ETL 2023 identified public administration as the most targeted sector (~19%), followed by targeted individuals (~11%), health (~8%), digital infrastructure (~7%) and manufacturing, finance and transport.
• Information manipulation has been as a key element of Russia’s war of aggression against Ukraine has become prominent.
• State-nexus groups maintain a continued interest on dual-use tools (to remain undetected) and on trojanising known software packages. Cybercriminals increasingly target cloud infrastructures, have geopolitical motivations in 2023 and increased their extortion operations, not only via ransomware but also by directly targeting users.
• Social engineering attacks grew significantly in 2023 with Artificial Intelligence (AI) and new types of techniques emerging, but phishing still remains the top attack vector.
The key findings and judgments in this assessment are based on multiple and publicly available resources which are provided in the references used for the development of this document. The report is mainly targeted at strategic decision-makers and policy-makers, while also being of interest to the technical cybersecurity community.
1.1 PRIME THREATS A series of cyber threats emerged and materialised during the reporting period. According to the findings detailed in this report, the ENISA Threat Landscape 2023 report highlights and directs attention toward eight prime threat groups (refer to Figure 1). These particular threat groups have been singled out due to their prominence over the years, their widespread occurrence and the significant impact resulting from the realisation of these threats.
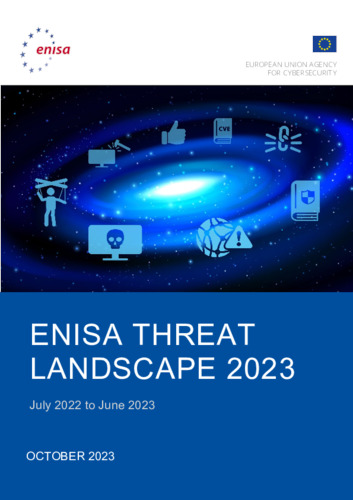
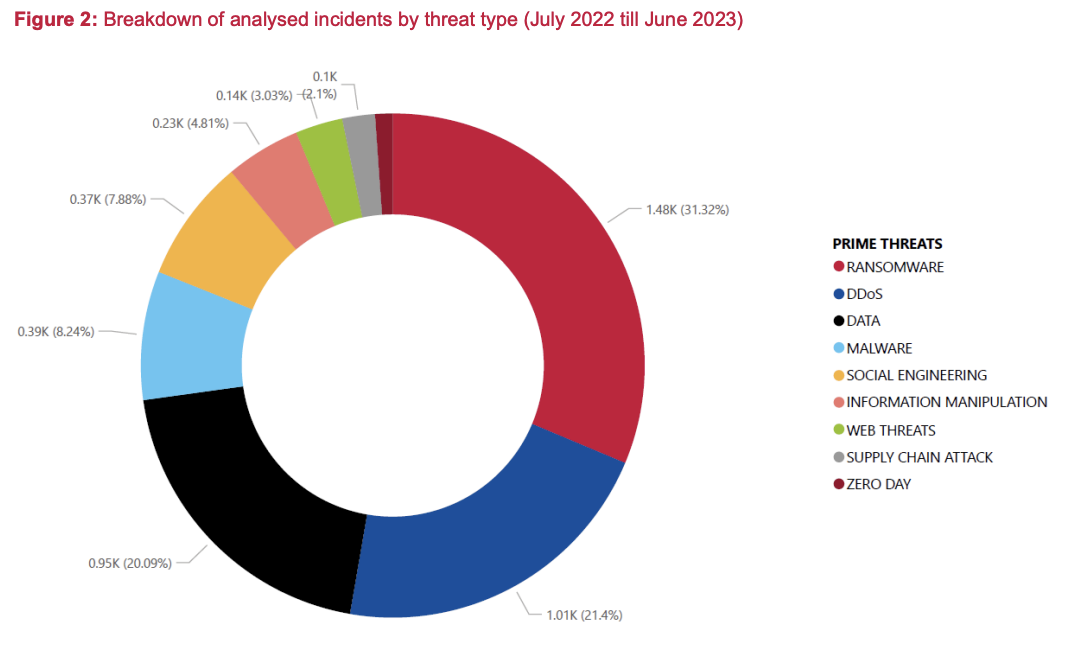
• Ransomware According to ENISA’s Threat Landscape for Ransomware Attacks3 report, ransomware is defined as a type of attack where threat actors take control of a target’s assets and demand a ransom in exchange for the return of the asset’s availability. This action-agnostic definition is needed to cover the changing ransomware threat landscape, the prevalence of multiple extortion techniques and the various goals, other than solely financial gains, of the perpetrators. Ransomware has been, once again, one of the prime threats during the reporting period, with several high profile and highly publicised incidents.
• Malware Malware, also referred to as malicious code and malicious logic, is an overarching term used to describe any software or firmware intended to perform an unauthorised process that will have an adverse impact on the confidentiality, integrity or availability of a system.
• Social Engineering Social engineering encompasses a broad range of activities that attempt to exploit human error or human behaviour with the objective of gaining access to information or services. It uses various forms of manipulation to trick victims into making mistakes or handing over sensitive or secret information. Users may be lured to open documents, files or e-mails, to visit websites or to grant access to systems or services. Although the lures and tricks used may abuse technology, they rely on a human element to be successful. This threat canvas consists mainly of the following attack vectors: phishing, spear-phishing, whaling, smishing, vishing, watering hole attack, baiting, pretexting, quid pro quo, honeytraps and scareware. While social engineering techniques are often used to gain initial access, they may also be used at later stages in an incident or breach. Notable examples are business e-mail compromise (BEC), fraud, impersonation, counterfeit and, more recently, extortion.
• Threats against data A data breach is defined in the GDPR as any breach of security leading to the accidental or unlawful destruction, loss, alteration or unauthorised disclosure of or access to personal data transmitted, stored or otherwise processed (article 4.12 GDPR). Technically speaking, threats against data can be mainly classified as data breach or data leak. Though often used as interchangeably concepts, they entail fundamentally different concepts that mostly lie in how they happen. Data breach is an intentional cyber-attack brought by a cybercriminal with the goal of gaining to unauthorised access and release sensitive, confidential or protected data. In other words, a data breach is a deliberate and forceful attack against a system or organisation with intention to steal data. Data leak is an event (e.g. misconfigurations, vulnerabilities or human errors) that can cause the unintentional loss or exposure of sensitive, confidential or protected data (intentional attacks are sometimes referred to as data exposure).
• Threats against availability: Denial of Service Availability is the target of a plethora of threats and attacks, among which DDoS stands out. DDoS targets system and data availability and, though it is not a new threat, it plays a significant role in the cybersecurity threat landscape. Attacks occur when users of a system or service are not able to access relevant data, services or other resources. This can be accomplished by exhausting the service and its resources or overloading the components of the network infrastructure.
• Threats against availability: Internet threats Threats to Internet availability refer to intentional or unintentional disruptions of Internet or electronic communications that result in Internet outages, blackouts, shutdowns or censorship. Internet disruptions can be due to government-directed Internet shutdowns, cyclones, massive earthquakes, power outages, cable cuts, cyberattacks, technical problems and military actions. These threats are diversifying and growing, having reached a new record in this reporting period and having caused huge monetary loss to national economies.
• Information Manipulation Foreign Information Manipulation and Interference (FIMI) describes a mostly non-illegal pattern of behaviour that threatens or has the potential to negatively impact values, procedures and political processes. Such activity is manipulative in character, conducted in an intentional and coordinated manner. FIMI can be carried out by state or non-state actors, including their proxies inside and outside of their own territory, whereas in this report we study the threat regardless of its origin.
• Supply Chain Attacks A supply chain attack targets the relationship between organisations and their suppliers. For this ETL report we use the definition as stated in the ENISA Threat Landscape for Supply Chain Attacks in which an attack is considered to have a supply chain component when it consists of a combination of at least two attacks. For an attack to be classified as a supply chain attack, both the supplier and the customer have to be targets. SolarWinds was one of the first revelations of this kind of attack and showed the potential impact of supply chain attacks. It was observed that threat actors are continuing to feed on this source to conduct their operations and gain a foothold within organisations, to benefit from the widespread impact and large victim base of such attacks.
Cyber threat actors are an integral component of the threat landscape. These are entities that aim to conduct malicious acts by taking advantage of existing vulnerabilities with the intention of harming their victims. Understanding how threat actors think and act as well as their motivations and goals are essential for a more robust management of cyber threats and better responses to incidents. Monitoring the latest developments concerning the tactics and techniques used by threat actors to achieve their objectives and staying up-to-date with the long-term trends in motivations and targets is crucial for an efficient defence in today’s cybersecurity ecosystem.
Moreover, understanding the trends related to threat actors, their motivations and their targets assists greatly in planning cybersecurity defences and mitigation strategies. It is an integral part of the overall assessment of threats since it allows security controls to be prioritised and a dedicated strategy based on potential impact and the likelihood that threats will materialise to be developed. Not understanding threat actors and how they operate creates a significant knowledge gap in cybersecurity because analysing threats without considering the motivations and goals may lead to inefficient defences or, in some cases, not being able to protect at all.
Cyber threat actors and their modus operandi are inevitably influenced by geopolitical events. A sizeable number of operations have been monitored, during the reporting period, where the actions of some cybercriminals, state-nexus threat groups and hacktivists have their roots in geopolitical developments. In general, at least state-nexus groups and hacktivists, regardless of motivation or agenda, can be triggered into action by these events. In this section, we explore the trends related to threat actors. This assessment does not provide an exhaustive list of all trends during the reporting period but rather a high-level view of the significant trends observed at a strategic level. We focus on the motives of threat actors, their impact, and targeting. Their evolution is also assessed.
For the ETL 2023 report, we consider once more the following four categories of cybersecurity threat actors:
• State-nexus threat groups, • Cybercriminals, • Hackers-for-hire, • Hacktivists.