Cisco 2017 Midyear Cyber Security Report Predicts New “Destruction of Service” Attacks; Scale and Impact of Threats Grow
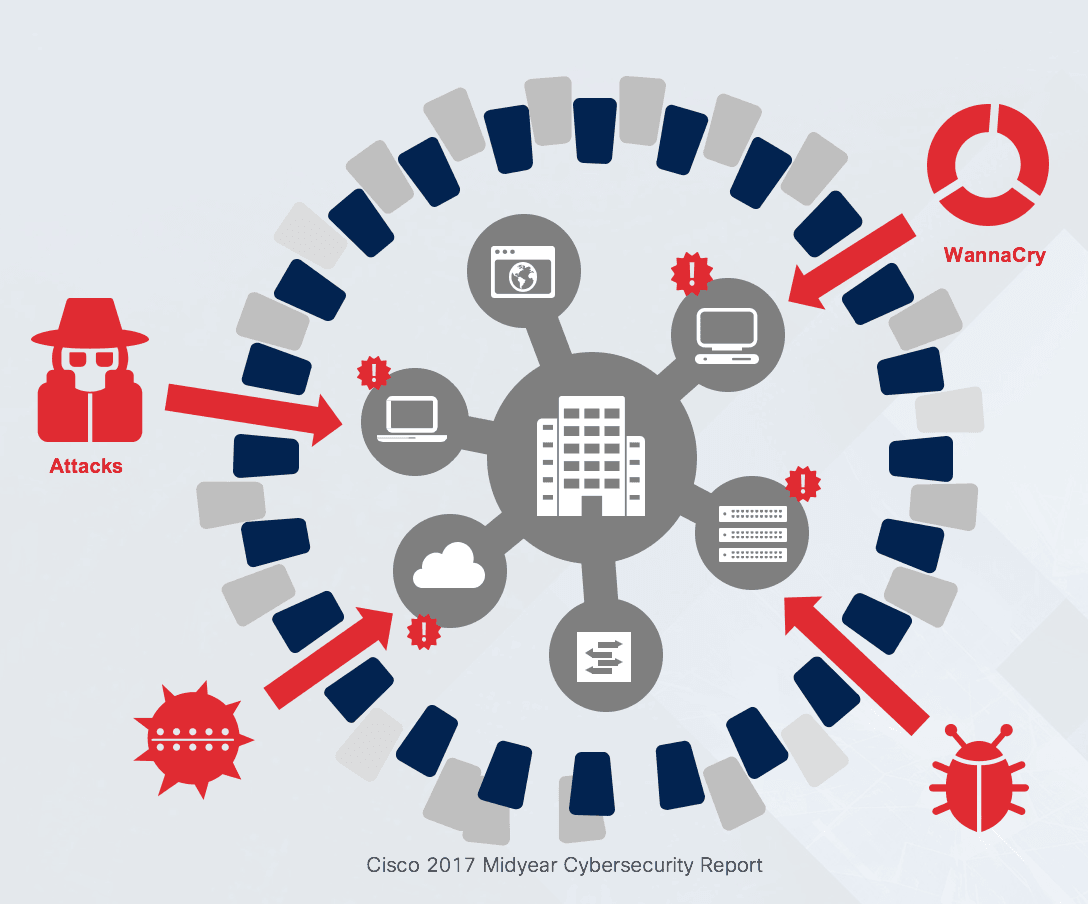
Last week, HSD partner Cisco released a 2017 Midyear Cybersecurity Report (MCR). The report uncovers the rapid evolution of threats and the increasing magnitude of attacks, and forecasts potential “destruction of service” (DeOS) attacks. These attacks - such as WannaCry and Nyetya - could eliminate organisations’ backups and safety nets, required to restore systems and data after an attack. Also, with the advent of the Internet of Things (IoT), key industries are bringing more operations online, increasing attack surfaces and the potential scale and impact of these threats.
As part of the Security Capabilities Benchmark Study, Cisco surveyed close to 3,000 security leaders across 13 countries and found that across industries, security teams are increasingly overwhelmed by the volume of attacks. This leads many to become more reactive in their protection efforts.
Important findings per industry include:
Public Sector – Of threats investigated, 32 percent are identified as legitimate threats, but only 47 percent of those legitimate threats are eventually remediated.
Retail – Thirty-two percent said they’d lost revenue due to attacks in the past year with about one-fourth losing customers or business opportunities.
Manufacturing – Forty percent of the manufacturing security professionals said they do not have a formal security strategy, nor do they follow standardised information security policy practices such as ISO 27001 or NIST 800-53.
Utilities – Security professionals said targeted attacks (42 percent) and advanced persistent threats, or APTs (40 percent), were the most critical security risks to their organisations.
Healthcare – Thirty-seven percent of the healthcare organisations said that targeted attacks are high-security risks to their organisations.
Cisco’s Advice for Organisations
- Keeping infrastructure and applications up to date, so that attackers can’t exploit publicly known weaknesses.
- Battle complexity through an integrated defense. Limit siloed investments.
- Engage executive leadership early to ensure complete understanding of risks, rewards and budgetary constraints.
- Establish clear metrics. Use them to validate and improve security practices.
- Examine employee security training with role-based training versus one-size-fits-all.
- Balance defense with an active response. Don’t “set and forget” security controls or processes.
Read the management summary.
More information in English or Dutch.
Want to know how to prevent or react in case of a cyber attack? Visit the CSW17 from 25-29 September in The Hague, with more than 70 cyber security events: www.cybersecurityweek.nl