Better Security Operational Technology (OT) Systems Needed
Manufacturing processes grinding to a halt. Robots that suddenly build something different or spray the wrong color. It could become a reality if boards of directors don’t pay attention to making their operational technology more secure. The OT Community of Practice (CoP) brings together knowledge and expertise.
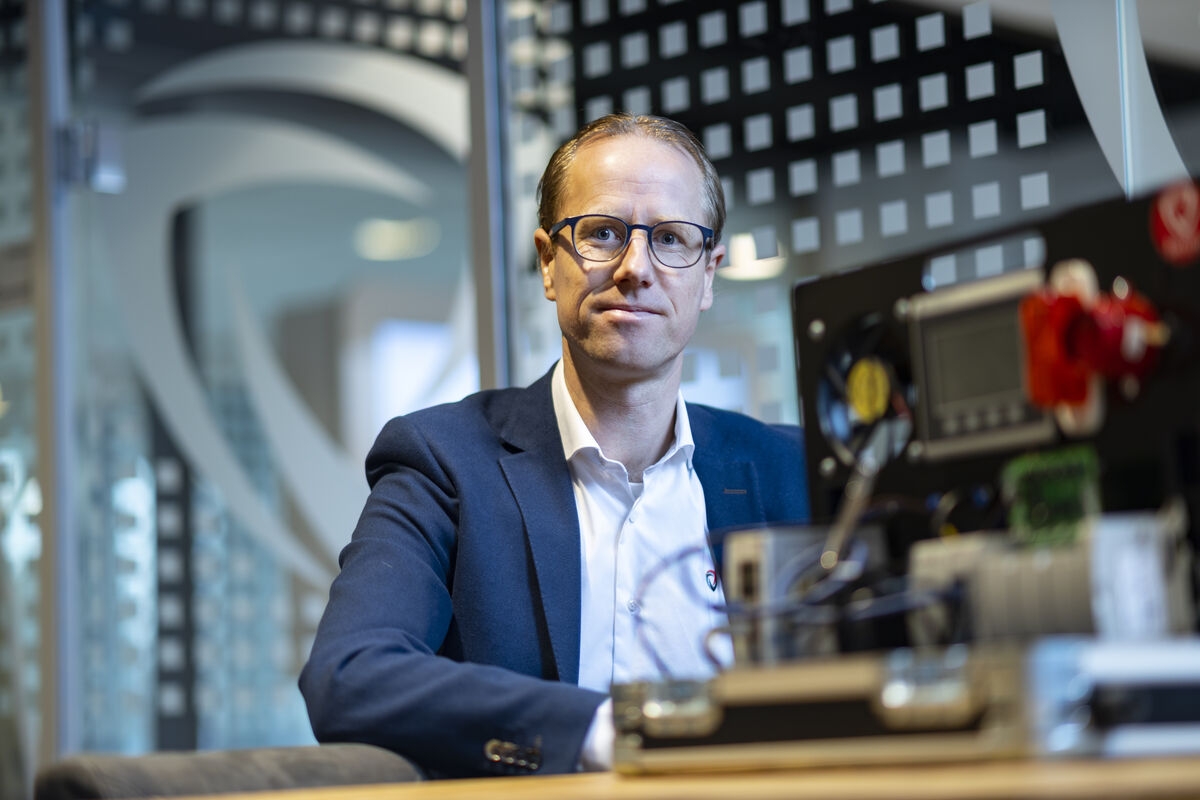
Industrial systems such as ICS and SCADA control physical business and production processes. These processes are becoming increasingly digitised and/or connected to the internet for the enormous opportunities involved. Sjoerd Peerlkamp from Secura explains that digitisation can for example improve maintenance, making production lines less likely to shut down. ‘’You can measure the vibrations of an engine and send the data digitally to the technical department. If the vibrations deviate too much from the average, it’s time to quickly replace the motor or to carry out maintenance.’’ Another example that Peerlkamp gives is energy management. ‘’The grid operator can lay extra thick cables to absorb all energy peaks, which is extremely expensive, or ensure that systems are temporarily switched off during peaks with careful measuring and switching. This saves huge investments, but also introduces new cyber risks.’’ Most automation within industrial systems has never considered the associated security. But now that more and more systems are connected to each other and the internet, the associated cyber risks are also increasing sharply.
OT-ransomware
The digital security of operational technology (OT) is still in its infancy. That’s not surprising, says Peerlkamp. ‘’OT systems last a very long time. They are therefore increasingly provided with online connections. But updating, patching, and securing is complicated. If you shut down an office system for an update, you can always print your report later or postpone your financial transactions for a while. But you don’t completely shut down a factory for an update. That costs a lot of money and involves risks when restarting. Everything is geared towards keeping the machines running, that’s the main priority.‘’ Peerlkamp therefore expects ransomware to be the biggest current threat to OT systems. Production processes are shut down and taken hostage or there is a threat to reset production robots to different settings. The cybercriminal wants you to pay for the ability to restart your own system.
Peerlkamp: ‘’The recovery time of a hacked OT system is many times greater than restoring a backup in the office environment. Semi-finished products can even have solidified while in a pipeline, so they will have to be replaced in the event of an attack. Due to the large losses when a production line is stopped, companies will be more likely to pay and will be willing to pay large sums for it. It is important to anticipate this and to put cybersecurity risks for operational processes high on the agenda of the management and to take appropriate measures as explained in, for example, IEC 62443.’’
Community of Practice
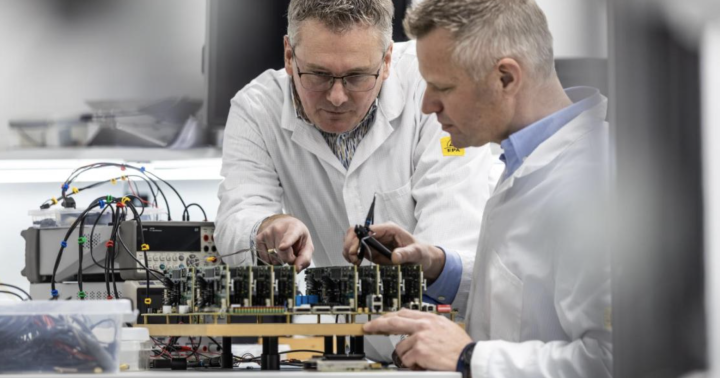
The available countermeasures vary widely. For example, it is possible to create safety zones based on risks and to separate them from each other. In addition, detection of deviating patterns is possible. ‘’OT systems are fairly predictable, so it’s relatively easy to control’’, says Peerlkamp. Just like other risks, cybersecurity risks should also be part of the risk management processes, so that conscious choices are made as to which risks are tackled and which risks are accepted. ‘’In addition, it is interesting to participate in HSD’s Community of Practice OT security.’’
This community consists of various companies and organisations involved in OT, both from the public and private sector. Since OT-security is not talked about enough, the CoP works on putting the topic higher on the agenda by hosting expert sessions and building an OT-security knowledge platform. During the expert sessions, a specific OT-security issue is discussed in more detail. This way organisations can share knowledge, experiences and learn from each other. In addition, the CoP posts relevant OT-security whitepapers, blogs and other content on the Security Insight knowledge platform. Via this platform, you can stay up to date on the latest OT-security updates and developments.
This way we can use and build upon each other’s expertise. For example, Secura has looked at all OT-related incidents in recent years and has made a trend analysis of techniques that hackers use to enter OT systems. This way others can arm themselves against these incidents. HSD is now also looking at connecting the expertise of the CoP with specific sectors such as the horticulture. For the time being, there is still plenty to do in this area and in the Netherlands.
NIS2
Improving the cyber security of OT systems will soon have a legal incentive as well. The European Parliament has recently adopted a cybersecurity legislation which will come into effect October 2024. This legislation, named NIS2 (Network and Information Security 2), is the successor of the original NIS from 2016 and mandates a cyber security baseline for organisations of a certain size operating within the European Union in certain industries.
Organisations that fall under NIS2 must, among others, assess and manage their cybersecurity risks, make sure their management receives adequate training, and have well defined policies and procedures that describe their cybersecurity posture. One way or another, they have to demonstrate that they take appropriate measures to counter their specific cyber security risks. If they do not have these things in order, they could face fines up to €10 million or 2% turnover (whichever is higher) depending on how the organisation is classified by NIS2.
Moreover, management can be held directly liable when negligence is proved after a successful cyber-attack. Bart Groothuis, the European Parliament’s Rapporteur for NIS2, hopes that these measures will make cybersecurity a board room issue and in turn accelerate the maturing of cybersecurity on all fronts, including industrial systems.
Would you like to know more about the Community of Practice? Visit our knowledge platform Security Insight. Here you will also find the latest OT Security trends and developments in the form of webinars, events, blogs, podcasts, and reports.